PDF files can be weaponized by malicious actors to steal Windows credentials (NTLM hashes) without any user interaction, and only by opening a file, according to Assaf Baharav, a security researcher with cyber-security Check Point.
Baharav published research this week showing how a malicious actor could take advantage of features natively found in the PDF standard to steal NTLM hashes, the format in which Windows stores user credentials.
"The PDF specification allows loading remote content for the GoToE & GoToR entries," Baharav told Bleeping Computer today.
Stealing Windows credentials via PDF and SMB
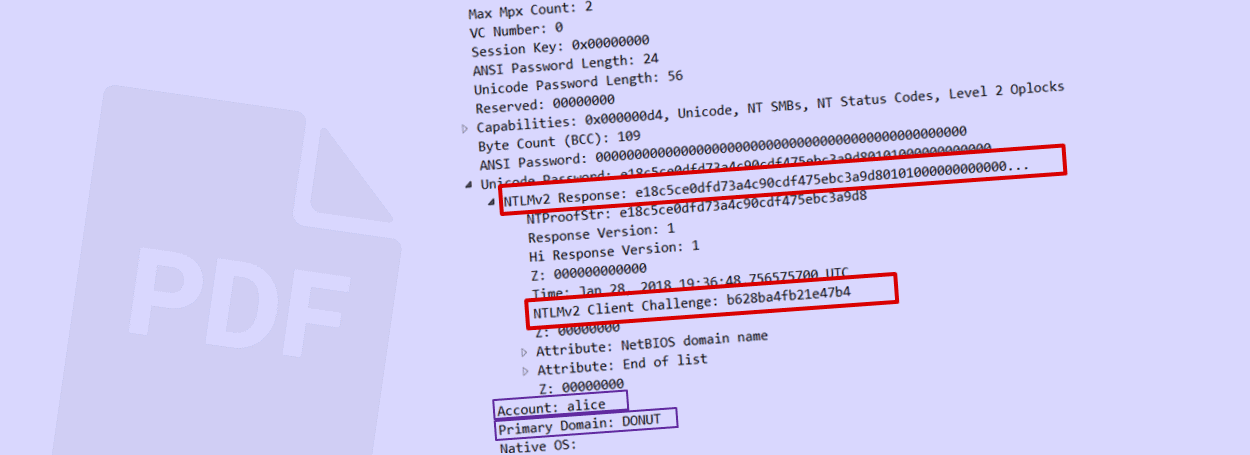
For his research, Baharav created a PDF document that would utilize these two PDF functions. When someone would open this file, the PDF document would automatically make a request to a remote malicious SMB server.
By design, all SMB requests also include the NTLM hash for authentication purposes. This NTLM hash would be recorded in the remote SMB server's log. Tools are available that can break this hash and recover the original password.
This type of attack is not new, at all, and in the past, has been executed by initiating SMB requests from inside Office documents, Outlook, browsers, Windows shortcut files, shared folders, and other Windows OS internal functions.
All PDF readers are most likely vulnerable
Now, Baharav has shown that PDF files are just as dangerous. The Check Point researcher told Bleeping Computer that he only field-tested the attack on Adobe Acrobat and FoxIT Reader.
"We chose to test these two high profile PDF readers," Baharav told us. "Regarding the others, we highly suspect they may be vulnerable as well."
"We followed a 90 days disclosure policy by notifying only Adobe and Foxit regarding the issues," Baharav says.
While FoxIT did not reply, Adobe said it doesn't plan to modify its software, deferring to Windows OS-level mitigations. Adobe engineers were referring to Microsoft Security Advisory ADV170014, released in October 2017.
Microsoft released ADV170014 to provide a technical mechanism and instructions on how users could disable NTLM SSO authentication on Windows operating systems, in the hopes of stopping the theft of NTLM hashes via SMB requests made to servers located outside the local network.
"The best practice here is to follow Microsoft optional security enhancement," Baharav told us.

.jpg)
Comments
gphill4 - 5 years ago
"...Adobe said it doesn't plan to modify its software, deferring to Windows OS-level mitigations. Adobe engineers were referring to Microsoft Security Advisory ADV170014, released in October 2017."
This seems crazy to me. You have to manually go to a Microsoft Security TechCenter webpage and agree to their EULA, download the patch for your OS version, then run it. While maybe this works as workaround for security aware users, how does it help protect the vast majority of people opening PDF files? Or isn't this type of attack likely to become widespread?
campuscodi - 5 years ago
Kinda yes. Adobe implemented the PDF standard as written. It's not its fault that Windows sends NTLM hashes with SMB requests outside of a local network.
ejhonda - 5 years ago
It's not even a patch, but a specified reg key deployment and then implementing a "network isolation policy". On top of that, MS isn't addressing it on anything other than their latest platforms (i.e. Win 10 and WinSvr 2016). This one won't be easy to slap on and legacy OSes are out in the cold.
michael43 - 5 years ago
So, nothing about the PDF viewer in Chrome? In Firefox? How about Sumatra PDF viewer?
ejhonda - 5 years ago
From Check Point's summary: "Our investigation lead us to conclude that all Windows PDF-viewers are vulnerable to this security flaw and will reveal the NTLM credentials."
John Dod - 5 years ago
While it may not be a perfect solution, it is typically best practice to block those ports outbound on your company or home firewall.